Track Manual Compliance tasks with AWS Config Process Checks
Need to make sure that manual tasks have been completed against your compliance framework? AWS Config Process Checks can help.

Unfortunately, not everything can be automated as much as we would like. This can be especially true when it comes to the world of compliance. Even in the AWS ecosystem, there is still a lot of things that don’t have an API we can query and require good old fashion manual clicking.
Some great examples of this are:
- Making sure the security contact information is configured on the AWS Account
- Making sure you have setup the security challenge questions on the AWS Account
We even have an extra challenge when working in hybrid environments and the physical world. How do we track that we have put a process in place to store our backup media in an offsite storage location?
Before we go to much further, some quick background info on the services and features we are talking about.
AWS Config
AWS Config is a service that records how resources are configured in AWS over time. This allows you to see how things have changed but also configure AWS Config Rules, which can monitor these resource changes and evaluate whether that resource is still compliant with your rules or now not compliant. You can then send alerts or take automated remediation actions.
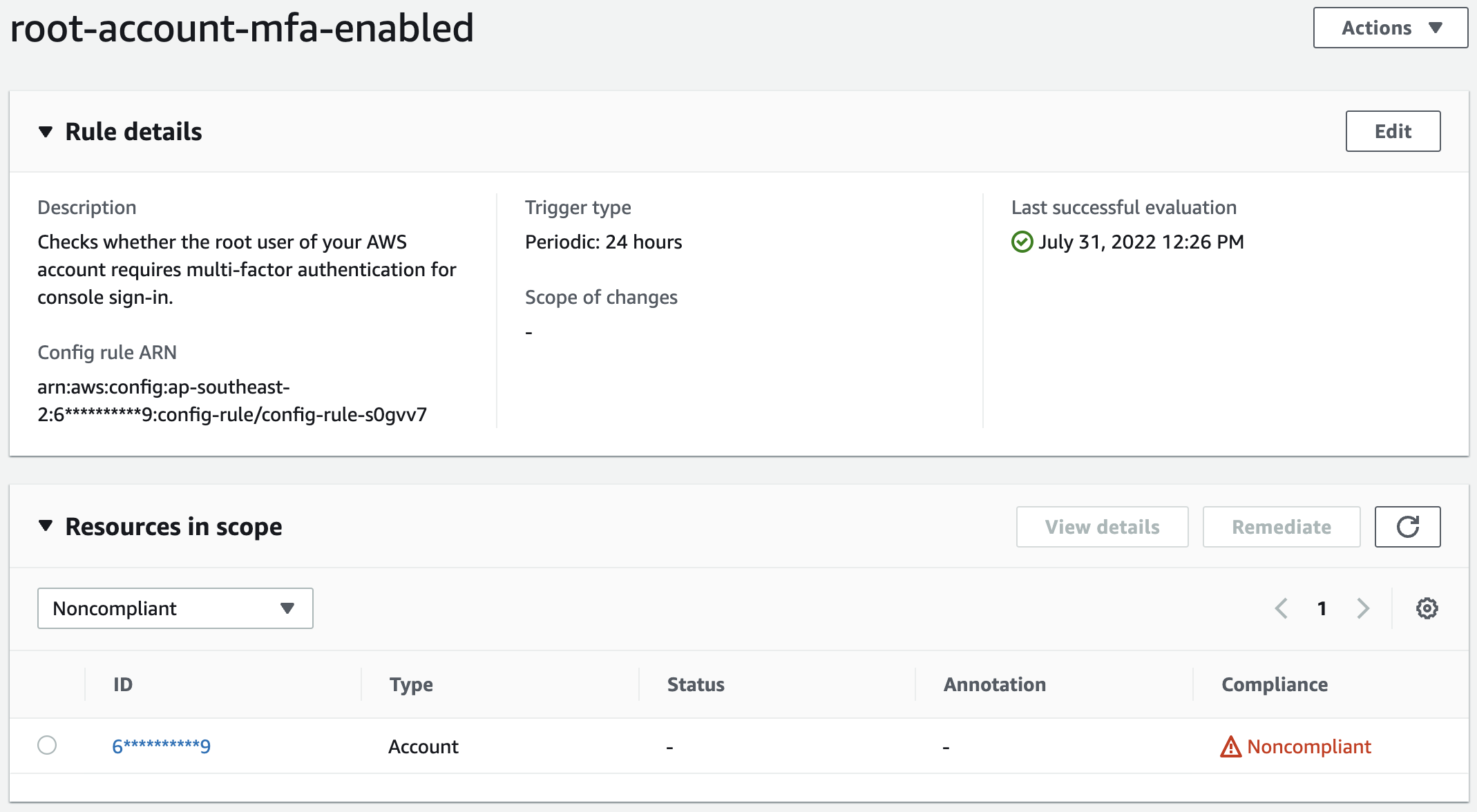
For example, here is an AWS Config rule provided by AWS to check if the root user has MFA enabled for console sign-in.
AWS Config Conformance Packs
AWS Config Conformance Packs are a grouping of AWS Config rules. They are kind of like CloudFormation templates but for AWS Config rules. Conformance packs allow you to deploy out all of your required AWS Config rules at once and manage them together.
The Solution: AWS Config Process Checks
Using AWS Config Conformance Packs, you can deploy special AWS Config Rules called Process Checks. These Process Checks allow you to create AWS Config Rules that can’t be automatically evaluated by AWS Config itself.
First, let’s have a look at a bit of a template for a Process Check
#Conformance Pack - Process Check Template
Resources:
AWSConfigProcessCheck:
Properties:
ConfigRuleName: ConfigRuleName
Description: Description of Config Rule
Source:
Owner: AWS
SourceIdentifier: AWS_CONFIG_PROCESS_CHECK
Type: AWS::Config::ConfigRule
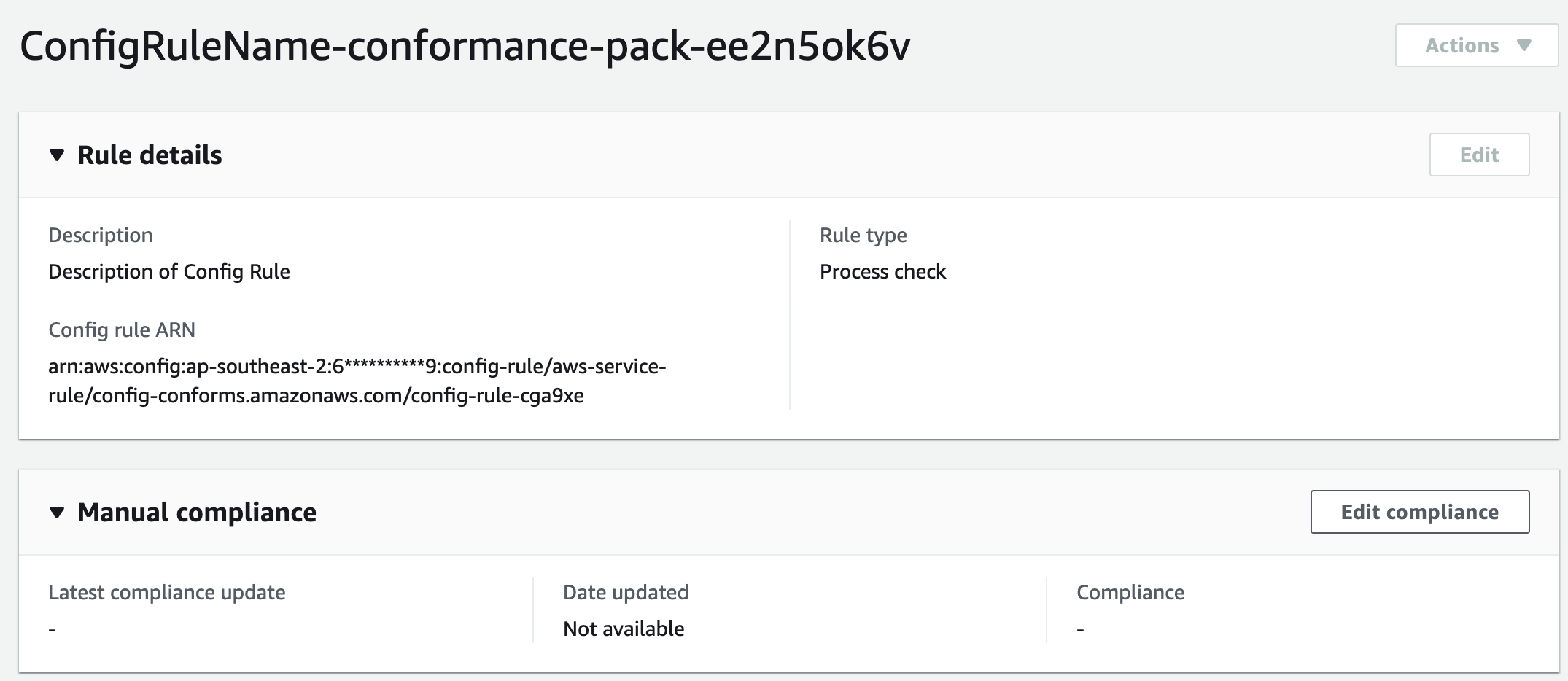
As you can see, it’s pretty simple to add a Process Check, simple just give it a name and description. In the console, this template will create a rule looking like this
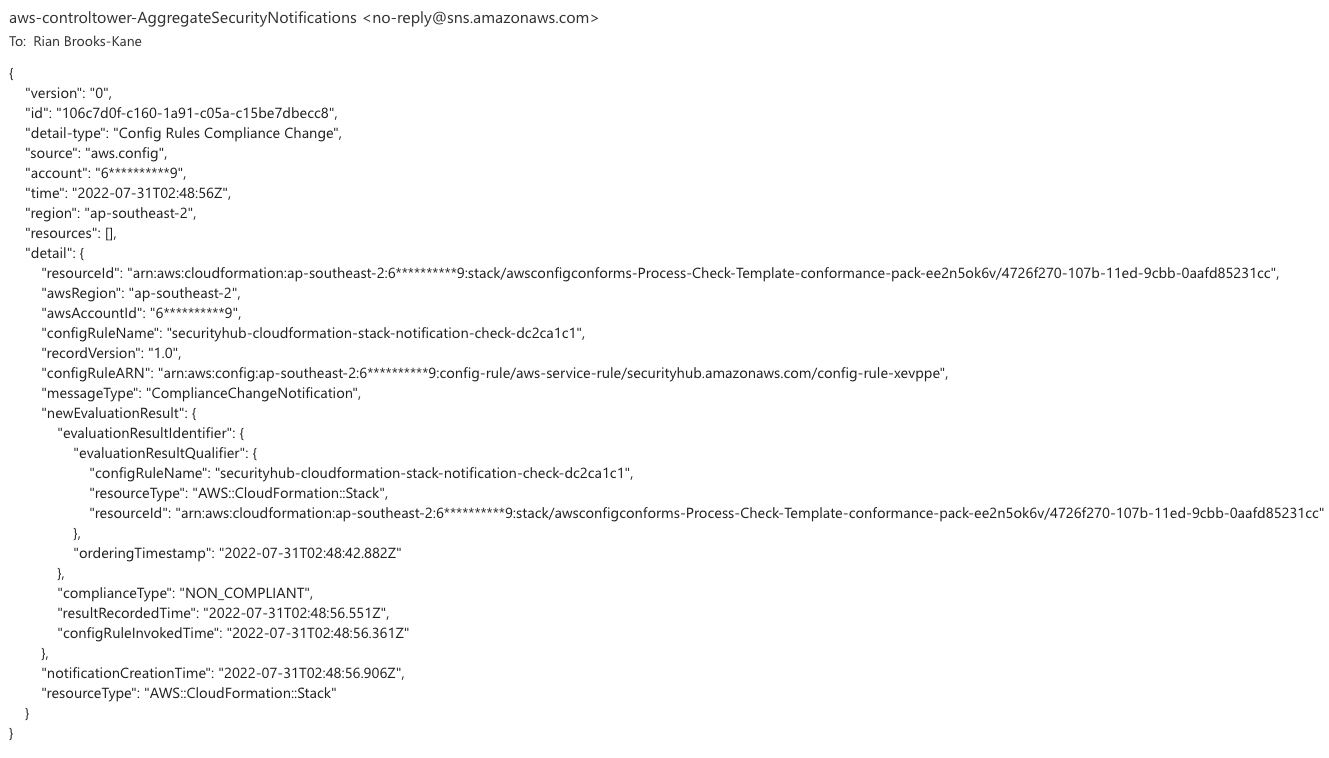
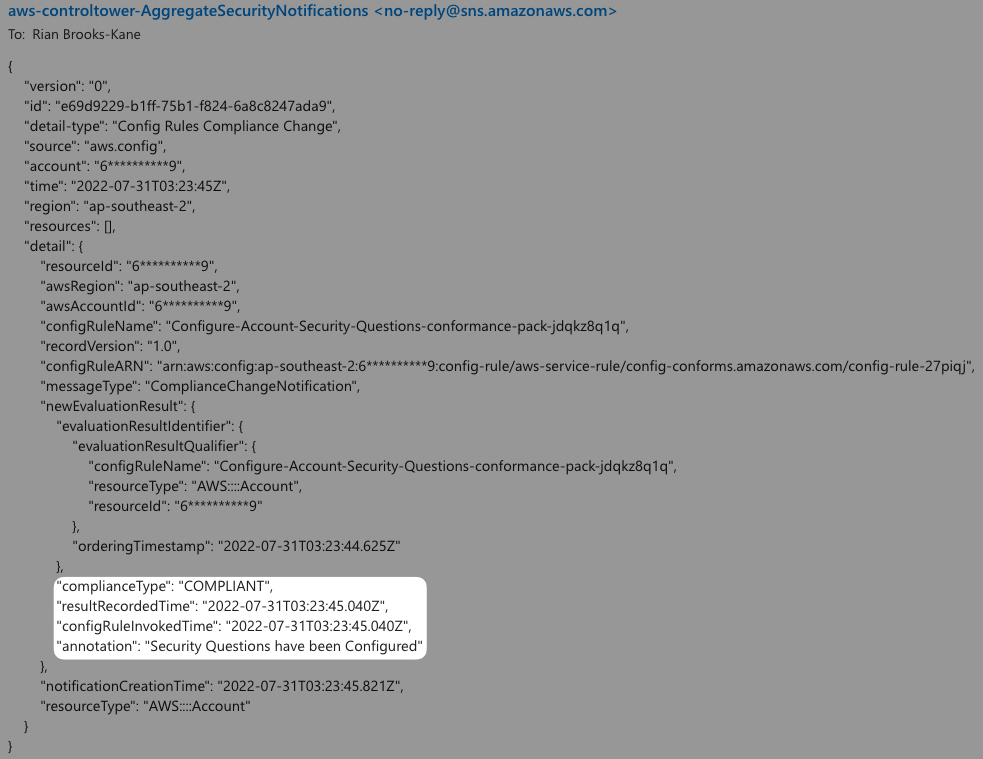
Because I also have alerts configured for AWS Config, I received the following alert too
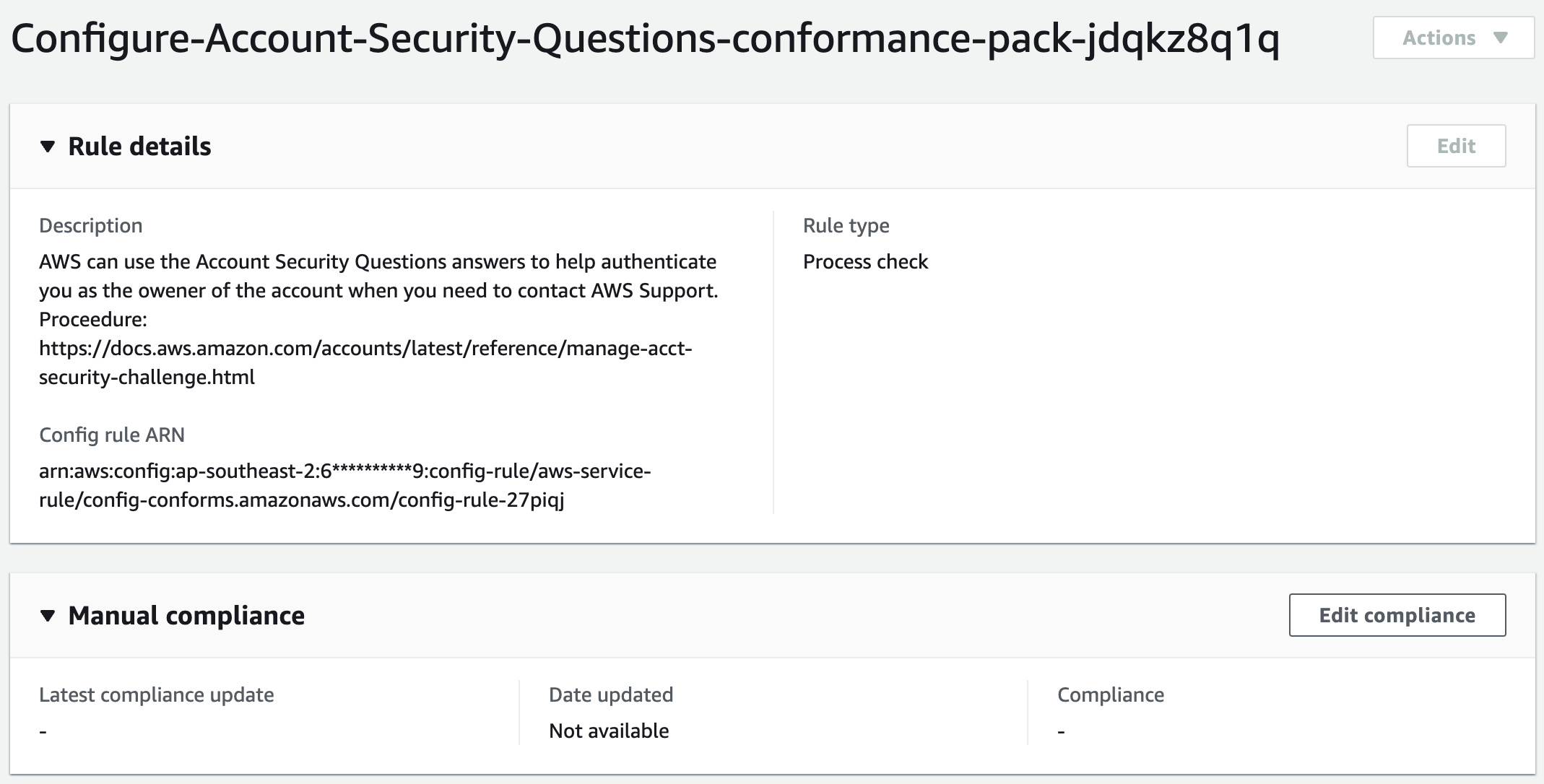
Let’s have a look at one of our examples from before: Making sure we have setup the security challenge questions on the AWS Account.
First, using the template we create the YAML template to make sure someone configures the security challenge questions.
#Conformance Pack - Process Check for Account Security Questions
Resources:
AccountSecurityQuestions:
Properties:
ConfigRuleName: Configure-Account-Security-Questions
Description: "AWS can use the Account Security Questions answers to help authenticate you as the owener of the account when you need to contact AWS Support. Proceedure: https://docs.aws.amazon.com/accounts/latest/reference/manage-acct-security-challenge.html"
Source:
Owner: AWS
SourceIdentifier: AWS_CONFIG_PROCESS_CHECK
Type: AWS::Config::ConfigRule
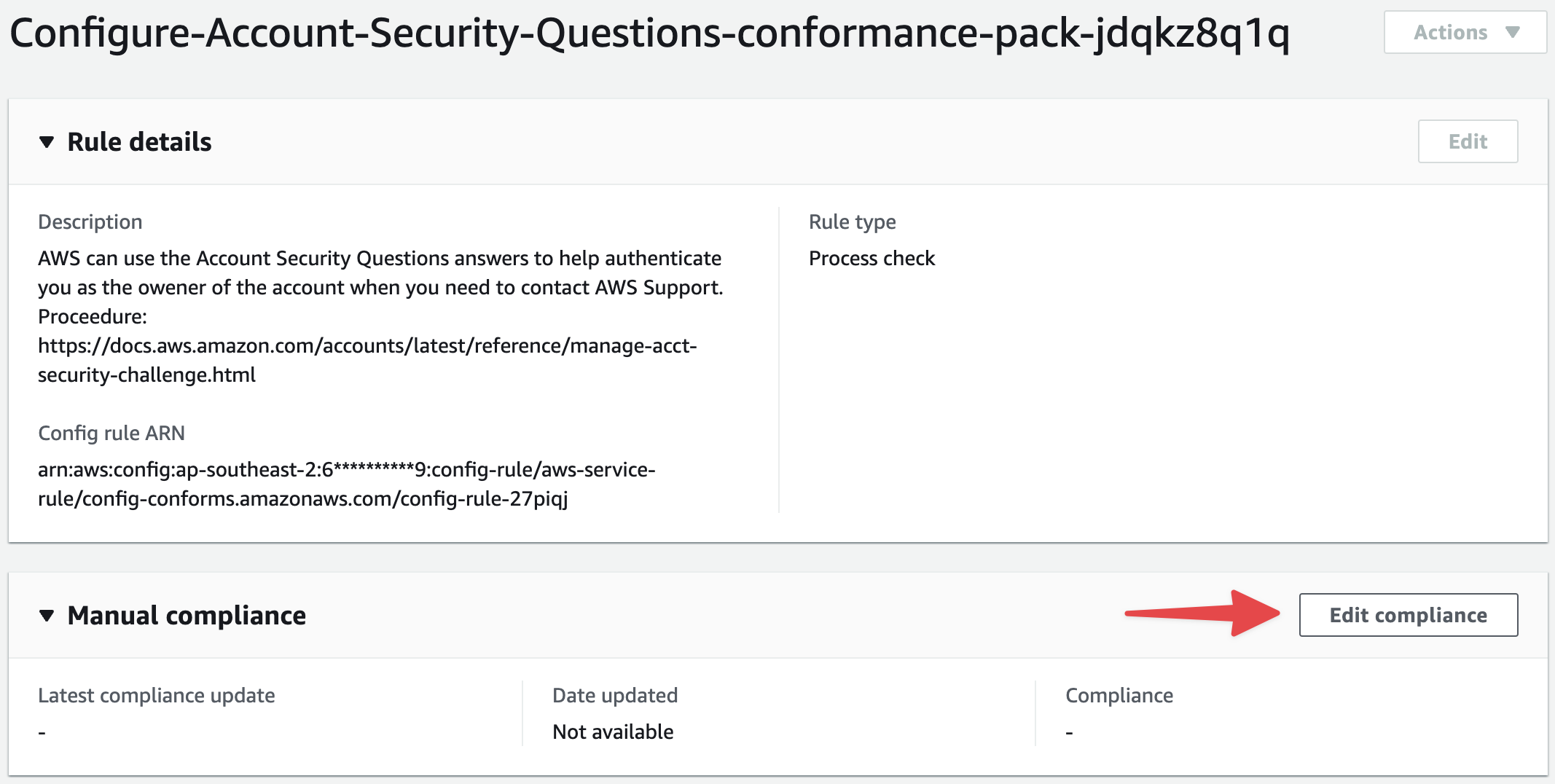
Once the compliance pack is uploaded, our rule is ready for us to change the compliance status.
Updating the compliance status
Luckily, there are three ways we can update the compliance status of a Process Check, and they aren’t all manual either! So if you have some automation for say a on-premise activity, you could easily automate the update of this check in AWS Config.
The three ways we can update the compliance status are:
- AWS Console
- CLI
- API
Updating compliance from the AWS console.
Click Edit compliance
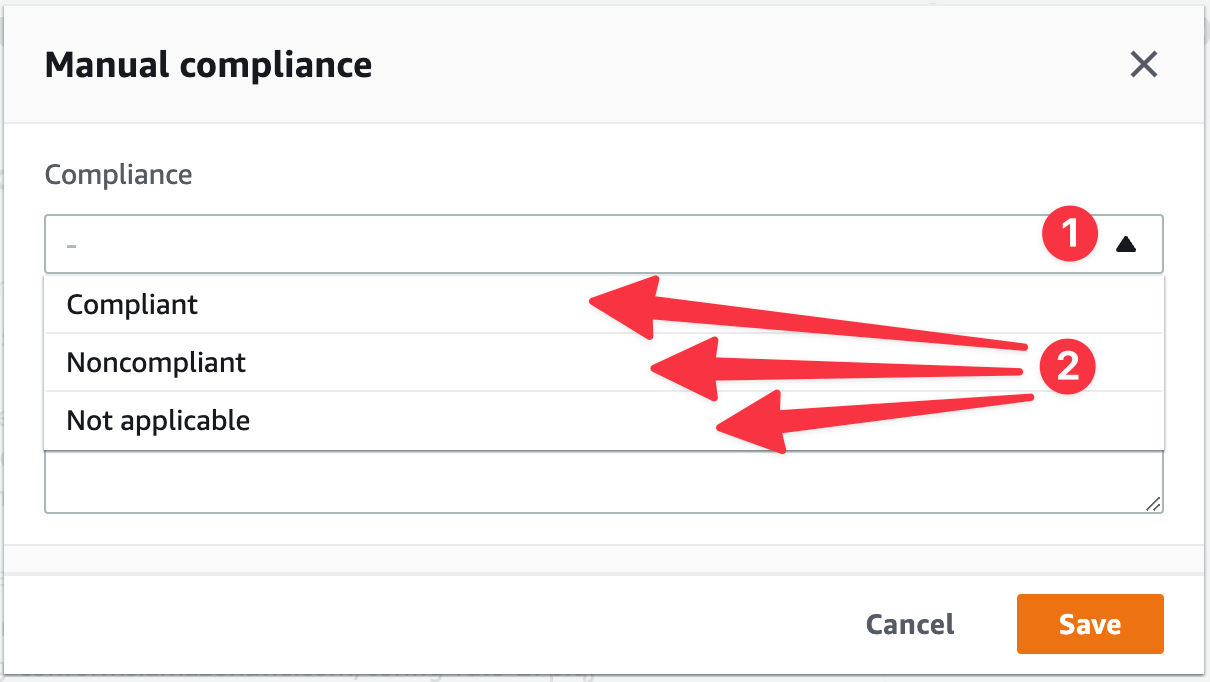
Select your compliance status.
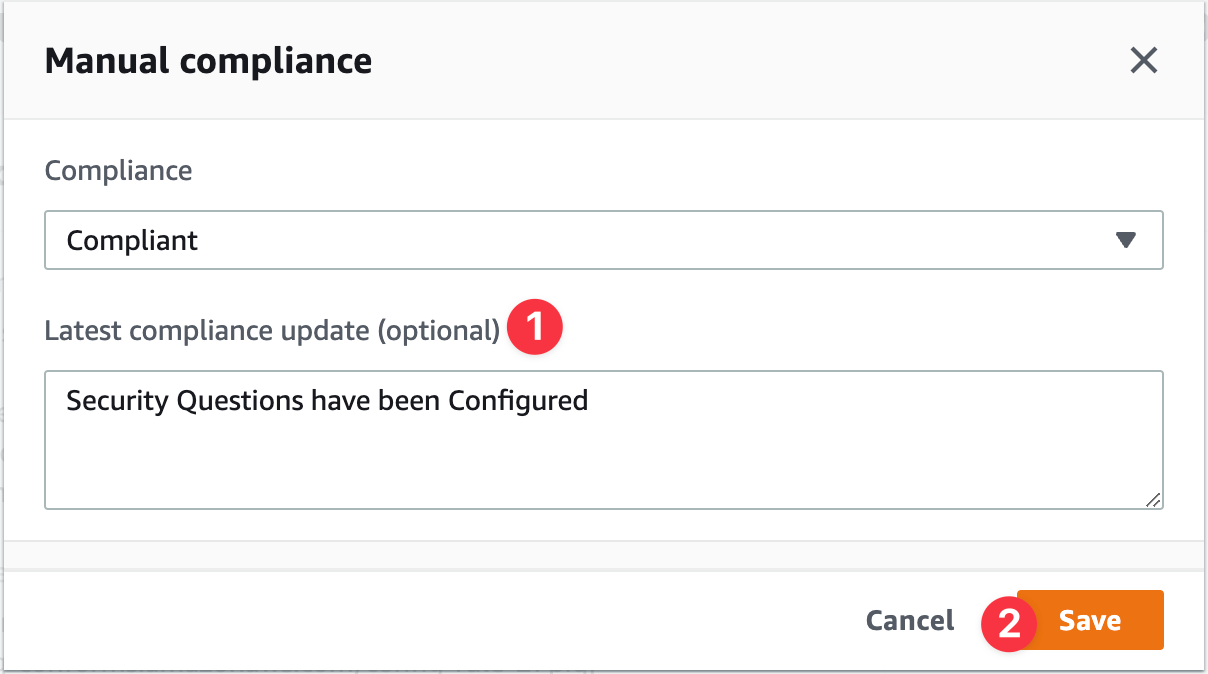
Type a note if you want and click Save.
As you can see, it has updated in the console.
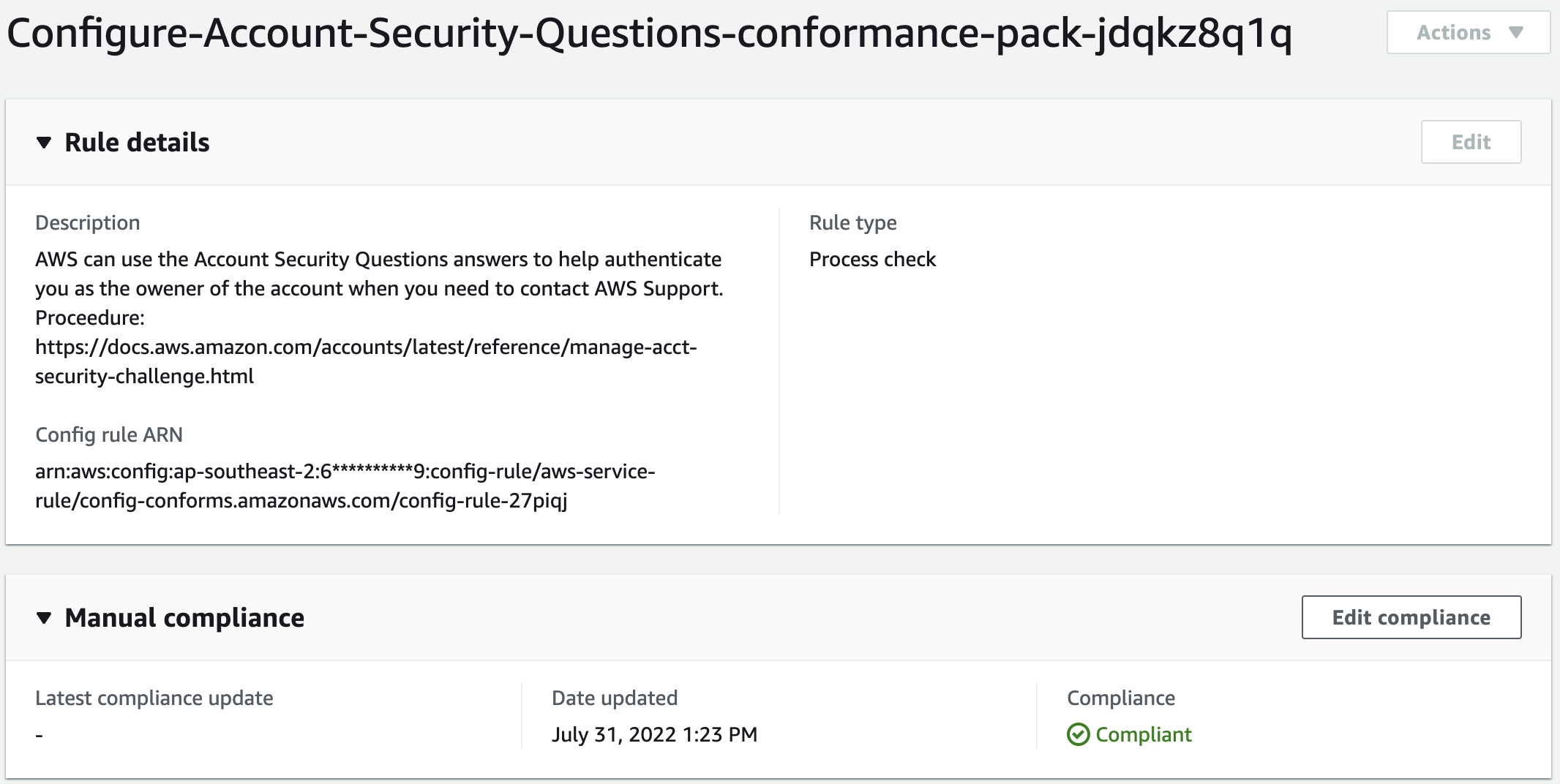
And you even get an email alert saying the check has now been marked compliant.
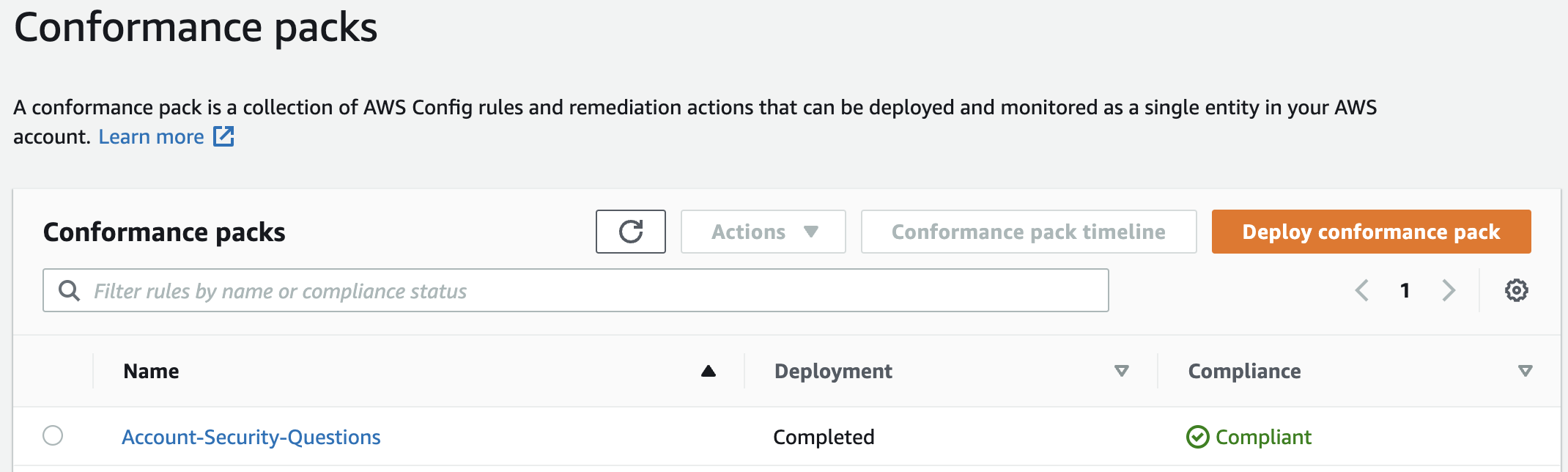
If I take a look at my conformance packs in the AWS Config console, I can see that this conformance pack is now fully compliant!
Holistic Compliance
AWS Config is a great tool for making sure you are following compliance when operating in AWS. Process Checks extend its capability to make sure you can also track any manual tasks required allowing you to monitor, track and report all of your compliance from one place.